Cybersecurity researchers have disclosed multiple vulnerabilities in a third-party driver software developed by Eltima that have been “unwittingly inherited” by cloud desktop solutions like Amazon Workspaces, Accops, and NoMachine and could provide attackers a path to perform an array of malicious activities.
“These vulnerabilities allow attackers to escalate privileges enabling them to disable security products, overwrite system components, corrupt the operating system, or perform malicious operations unimpeded,” SentinelOne researchers said in a report shared with The Hacker News.
The flaws have since been addressed in Amazon Nimble Studio AMI, Amazon NICE DCV, Amazon WorkSpaces, Amazon AppStream, NoMachine, Accops HyWorks, Accops HyWorks DVM Tools, Eltima USB Network Gate, Amzetta zPortal Windows zClient, Amzetta zPortal DVM Tools, FlexiHub, and Donglify.
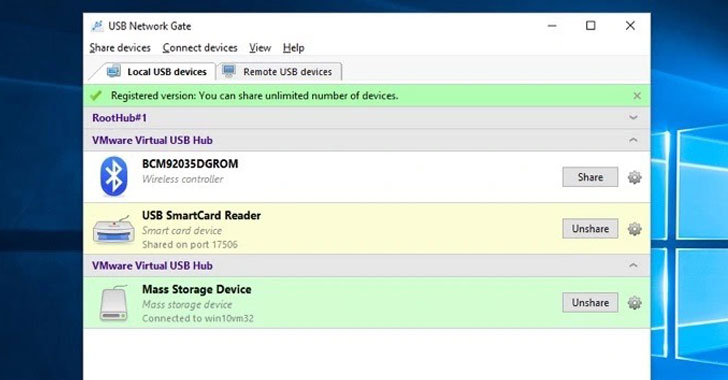
At its core, the issues reside in a product developed by Eltima that offers “USB over Ethernet” capabilities, and enables desktop virtualization services like Amazon WorkSpaces to redirect connected USB devices such as webcams to their remote desktop.
Specifically, the vulnerabilities can be traced back to two drivers that are responsible for USB redirection — “wspvuhub.sys” and “wspusbfilter.sys” — leading to a buffer overflow scenario that could result in the execution of arbitrary code with kernel-mode privileges.
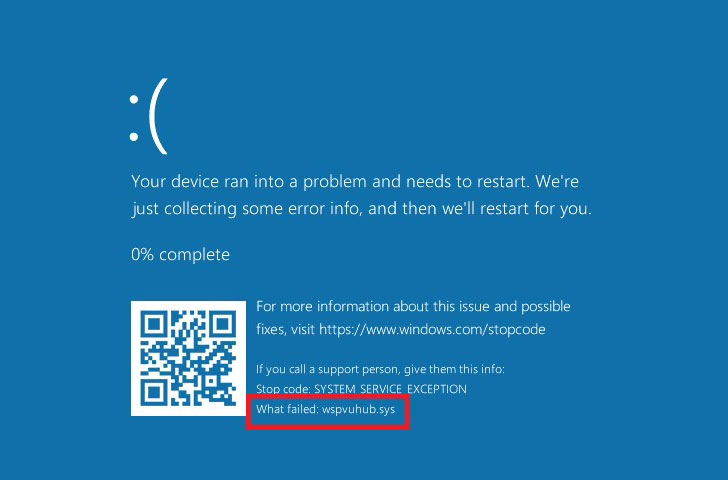 |
| BSoD Proof Of Concept |
“An attacker with access to an organization’s network may also gain access to execute code on unpatched systems and use this vulnerability to gain local elevation of privilege,” the cybersecurity firm noted. “Attackers can then leverage other techniques to pivot to the broader network, like lateral movement.”
The discovery marks the fourth set of security vulnerabilities affecting software drivers that have been uncovered by SentinelOne since the start of the year.
Earlier this May, the Mountain View-based company disclosed a number of privilege escalation vulnerabilities in Dell’s firmware update driver named “dbutil_2_3.sys” that went undisclosed for more than 12 years. Then in July, it also made public a high-severity buffer overflow flaw impacting “ssport.sys” and used in HP, Xerox, and Samsung printers that were found to have remained undetected since 2005.
And in September, SentinelOne made public a high-severity flaw in the HP OMEN driver software “HpPortIox64.sys” that could allow threat actors to elevate privileges to kernel mode without requiring administrator permissions, allowing them to disable security products, overwrite system components, and even corrupt the operating system.